¶ What is Engineering Information Control?
The concept of engineering information control refers to process of managing and protecting sensitive engineering data and intellectual property throughout the design, development, and maintenance of a product or system. This involves implementing policies, procedures, and tools to ensure the confidentiality, integrity, and availability of engineering information while minimizing the risk of unauthorized access, theft, or tampering.
¶ Video Summary - Engineering Information Control
https://www.youtube.com/watch?v=yeDR2xOYVRk
¶ Why is it Important?
Engineering information includes sensitive details about security zones and the inner working of the site or system that the engineering documentation applies to. In the past, this information was largely proprietary and not well understood, but with the increasing connectivity with IT systems, standardization of technology and general availability of information on the internet, it has become increasingly challenging to protect this information. Here are a variety of risk factors to consider when deciding on the importance of protecting engineering information.
- Safeguarding critical infrastructure: Engineering information related to critical infrastructure, such as power plants, transportation systems, or water treatment facilities, can be targeted by malicious actors to plan and execute cyberattacks. Restricting access to this information helps protect critical infrastructure and maintain its security and resilience.
- Protection of intellectual property: Engineering information often contains valuable intellectual property, such as designs, schematics, specifications, and trade secrets. Unauthorized access to this information can lead to theft, misappropriation, or even reverse engineering of a product, which could undermine an organization's competitive advantage or lead to exploitation by adversaries.
- Confidentiality: Engineering information may contain sensitive business, financial, or client data that needs to be kept confidential. Unauthorized access to this information can lead to data breaches, damage to an organization's reputation, and potential legal liabilities as well as impacts to the organizations market positioning due to leakage of business plans.
- Compliance with regulations and standards: Organizations may be required to restrict access to engineering information to comply with industry standards, regulatory requirements, or contractual obligations. Failing to do so could result in fines, penalties, or loss of business opportunities. Examples of this include NERC CIP regulations, the TSA requiresments for the protection of sensitive Security Information (SSI) within airports and other transportation entities and many others.
- Security and integrity: Restricting access to engineering information helps maintain the integrity and security of the data. Unauthorized access could lead to tampering, manipulation, or corruption of the information, which can compromise the quality, safety, or effectiveness of the final product or system.
- Prevention of insider threats: Limiting access to engineering information based on the principle of least privilege helps prevent insider threats, where employees or contractors with access to sensitive information may intentionally or unintentionally cause harm to the organization.
- Business continuity: Protecting engineering information and ensuring its availability is essential for business continuity. Unauthorized access can disrupt operations, delay projects, or even result in the loss of critical data needed to maintain ongoing activities.
¶ How do we do it?
The most effective means of controlling engineering information is to reduce the amount of data to be protected, removing it from locations it is not needed, or destroying it once its purpose has been met.
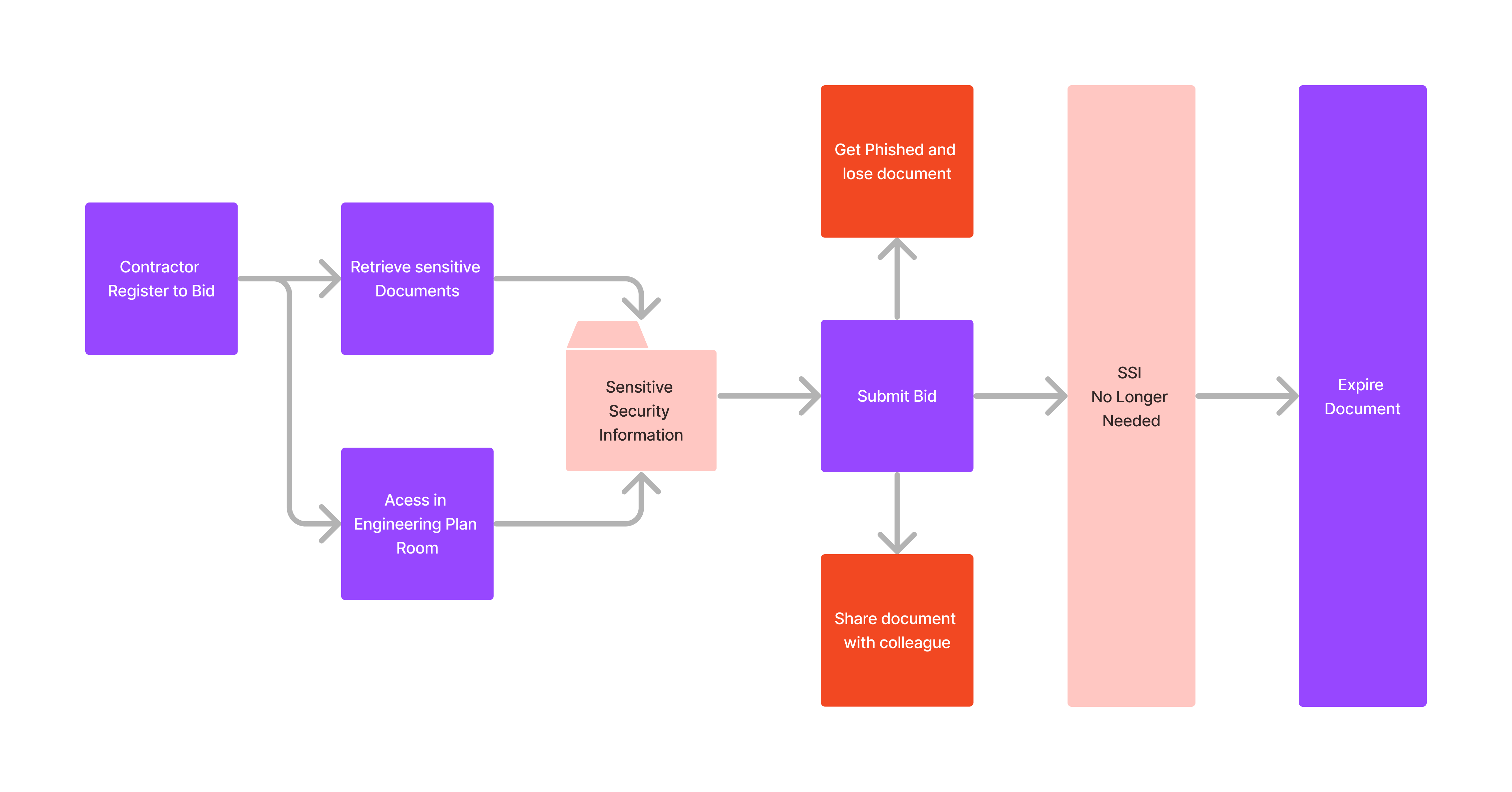
One common scenario in engineering is working with external engineering plan rooms and other engineering firms, where they need access to sensitive information to develop a bid package for a new construction project or they may be creating engineering documents as part of design. This can be challenging to control, as once the data leaves the confines of the critical infrastructure operator’s environment, it can be challenging to control. Below is one way we have seen this happen, and how we can leverage technologies such as Digital Rights Management to expire the document.
Here are a few ways you can try to reign that in, as well as control sensitive engineering information inside your organization.
- Digital rights management (DRM): Implement digital rights management solutions to control the access, distribution, and usage of sensitive documents. DRM systems can restrict actions like copying, printing, and editing, as well as enforce document expiration dates so the data can be rendered inaccessible once it is no longer needed.
- Document watermarking: Add watermarks to sensitive documents that indicate the document's confidentiality level and the recipient's identity. This can help deter unauthorized sharing and can trace leaked documents back to the source.
- Encryption: Encrypt sensitive documents, both at rest and during transmission, using strong encryption algorithms. This will protect the information from unauthorized access, tampering, or theft. Make sure to securely share the decryption keys or passwords with authorized recipients only. Consider the need for encryption mechanisms that will need to stand the test of time. The move towards post-quantum (or quantum resistant) cryptography may make sense in this context, as an engineering document created today, may still need protection 20 years from now.
- Access control: Implement strict access control measures, such as role-based access control, multi-factor authentication, and the principle of least privilege. Ensure that only authorized personnel can access the sensitive documents. Identity based approaches such as those leveraged by zero trust architectures can also be an effective means of controlling access.
- Secure file transfer protocols: Use secure file transfer protocols, such as SFTP (SSH File Transfer Protocol) or FTPS (FTP Secure), to transmit sensitive documents. These protocols provide secure channels for data transmission by encrypting the data during transit.
- Non-disclosure agreements (NDAs): Require external parties involved in the engineering construction bid process to sign NDAs, legally obligating them to maintain the confidentiality of sensitive information and not share it with unauthorized parties.
- Auditing and monitoring: Regularly audit and monitor access to sensitive engineering documents to identify and address potential security issues, such as unauthorized access or attempts to modify the data. Implement logging and alert mechanisms to notify relevant personnel of any suspicious activities. Leverage OSINT to identify when data has leaked onto the internet.
- Training and awareness: Provide training and raise awareness among internal staff and external parties involved in the engineering process about the importance of protecting sensitive engineering documents and following best practices for handling and securing the data.
- Version control and change management: Implementing version control and change management processes allows organizations to track and manage changes to engineering information, ensuring that only authorized modifications are made. This helps to maintain the integrity and consistency of the data and reduces the risk of errors or unauthorized alterations.
- Incident response and recovery: Developing and implementing incident response and recovery plans can help organizations quickly detect, respond to, and recover from security incidents involving engineering information. This helps to minimize the potential damage and ensure the continued availability of critical data.
- Secure disposal: Once the bidding process is completed, ensure that sensitive documents are securely disposed of by all parties involved. This may include secure deletion of electronic files and shredding of physical documents.
¶ When do we do it?
Data security is a continuous process, but there are some activities that are foundational for building the capability of your program to properly manage engineering information.
Data classification needs to happens fairly early in the process. if you don't have a definition of what sensitive information is, and do not have a process for clearly marking documents based on their data classification level, this all becomes extremeky challenging to implement.
Processes for data handling have to be defined, and this includes contracting and bid processes, working with engineering plan rooms, how the engineering documents flow to and from your organization and many more. One key challenge we have seen is related to the slowness of getting access to engineering documents, and difficulties when a document is “locked for editing” when security needs access to perform design validation. This cumbersome process can be made even more challenging without effective tools enabling this process.
¶ What resources can help?
This CIE principle includes a variety of technologies such as MFA, Access Control, Incident Response and more, but as some of them will factor into Secure Information Architecture and Resilient Layered Defense, we will instead focus on the technologies related to data security that are pertinent to Engineering Information Control such as Digital Rights Management and Secure Disposal.
Additionally, it can be very effective to use OSINT in discovery of this information, but we will also cover OSINT in a future article.
¶ Free and Open Source
Digital Right Management
There are no known full implementations of DRM that are open source. There are many DRM removal projects, but the open source community has not invested much time in this area.
Secure Disposal
¶ Commercial
Digital Right Management
Secure Disposal